As the adoption of electric vehicles (EVs) continues to rise, the charging infrastructure that supports this transformation must evolve. A critical aspect of maintaining a reliable and secure EV charging ecosystem is charging stations’ configuration management.
Enforcing the required charging station’s configuration not only impacts the safety and cybersecurity of the infrastructure but also plays a pivotal role in delivering a consistent and seamless charging experience for drivers.
Managing and monitoring charging stations’ configuration is essential for ensuring network reliability, preventing fraud, minimizing the potential attack surface and vulnerability exposure, and maintaining consistent charging experiences across different charging locations, vendors, and stations.
In this blog, we will explore why it is crucial to continuously manage the configurations of EV charging stations, the challenges associated with configuration management, and how real-time monitoring and alerts can help protect your infrastructure from vulnerabilities and misconfiguration exploitations.
The Power and Risks of Configuration Control in EV Charging Networks
Charging stations provide extensive configurations and operating options to support the different use cases of EV charging.
Through the Open Charge Point Protocol (OCPP) and vendor applications, Charge Point Operators (CPOs) have extensive control over their charging station configurations, allowing them to manage operations efficiently, enhance security, and optimize the user experience.
Utilizing protocols such as the OCPP, Charging stations enable real-time adjustments to various key settings, such as tariffs and pricing rules, power management policies, remote access and security configurations, user authentication methods, restricting free charging modes, and control of the station’s UI settings (screen brightness, UI language, etc.)
While this level of control provides flexibility and efficiency, poorly managed configurations can introduce serious security vulnerabilities and safety risks.
Misconfigurations—whether accidental or intentional—can lead to security vulnerabilities, safety hazards, and poor user experiences
The Challenge of Vendor-Specific Configurations
One of the biggest challenges in maintaining consistent configuration in the charging network is the lack of standardization across different charging station vendors.
Each manufacturer may define unique configuration parameters outside of the OCPP standard, making it difficult for CPOs to maintain a consistent security posture and operational framework.
For example, consider the following vendor-specific configurations that could pose a risk if not managed properly:
Custom Power Management Settings – Some chargers allow administrators to manually set power output limits. If misconfigured, this can lead to Denial-of-Charge (DoC), where a charger either fails to deliver power to EVs or overloads the site’s infrastructure.
Vendor-Specific Anti-Tampering Controls – Some chargers allow drivers to start a charging session even when the charger’s cabinet door is open. If enabled, this setting poses a serious safety risk by exposing internal components to unauthorized access, tampering, or electrical hazards.
Remote Access Settings – Some vendors provide default remote access credentials, which, if left unmanaged, can be exploited by hackers to take control of the charger.
Firmware Update Controls – Different chargers handle firmware updates differently. If left unmanaged, outdated firmware with known vulnerabilities can expose the charger to cyberattack
Because of these variations, CPOs must have full visibility into charger configurations and the ability to apply policies across all charging stations to ensure a unified and secure infrastructure.

7 Best Practices For Configurations Standardization
For a consistent and secure driver experience, all chargers at a given location or type should be configured according to the organizational policy.
When configurations vary between chargers at the same site, drivers may encounter issues such as inconsistent charging speeds, different payment methods, or even connectivity problems with the charging network.
To maintain a uniform and secure infrastructure, CPOs should follow key best practices for configuration management:
- Standardize Configuration Policies – Define and enforce a baseline configuration for all chargers to ensure uniform behavior and security settings.
- Implement Centralized Management – Use a centralized platform to monitor, update, and apply configurations across all charging stations.
- Enforce Secure Default Settings – Ensure that default settings (e.g., remote access, Free Vend, encryption protocols) are reviewed and hardened before deployment.
- Log and Audit Configuration Changes – Maintain a detailed audit log of all configuration modifications, including who made the change and when for compliance and security monitoring.
- Regularly Audit and Update Configurations – Periodically review settings to identify misconfigurations, update firmware, and align with security best practices.
- Enable Real-Time Monitoring and Alerts – Continuously track configuration changes and trigger alerts for unauthorized or unintended modifications.
- Vulnerability Management – Continuously monitor the charging network for known vulnerabilities that are applicable, given the charging network’s architecture, vendors and models.
By following these best practices, CPOs can ensure that all chargers operate consistently, enhancing security, reliability, and the overall EV driver experience.
The Safety Net: Real-Time Monitoring and Alerts
While maintaining consistent configurations is crucial, the ability to monitor and alert in real-time on any changes and alterations is equally important. Charging station configurations can sometimes change unintentionally during routine maintenance or software updates.
These accidental changes could lead to misconfigurations that leave charging stations vulnerable to fraudulent activities and exploitation by hackers or could even result in unsafe charging conditions for drivers.
Real-time monitoring ensures that CPOs are immediately notified when configuration changes occur. Alerts help detect misconfigurations before they cause significant issues, allowing operators to respond swiftly to prevent potential damage or downtime.
Moreover, continuous monitoring and alerting are essential components of the NIS2 regulation, which mandates stronger cybersecurity oversight for critical infrastructure, including EV charging networks.
By aligning the configuration of chargers on the same site, CPOs ensure:
- A uniform charging experience: All drivers will have the same expectations regardless of which charger they use.
- Reduced downtime: A consistent configuration means fewer errors and less troubleshooting, keeping the charging station running smoothly and efficiently.
- Better integration with backend systems: Uniform configurations make it easier to integrate with payment systems, monitoring tools, and data analytics platforms.
Configuration Management is Non-Negotiable
Managing EV charger configurations is not just a best practice—it’s a necessity for ensuring security, reliability, and a seamless charging experience.
CPOs must:
✅ Gain full visibility into all charger configurations, regardless of the vendor.
✅ Standardize configurations across all chargers in a site for a consistent user experience.
✅ Implement live monitoring and real-time alerts to detect unauthorized changes or misconfigurations before they cause harm.
Without proper configuration management, EV charging networks remain vulnerable to cyber threats, operational disruptions, fraudulent activities, and safety risks. As the industry evolves, well-managed configurations will be a key differentiator for CPOs looking to build a trusted and resilient charging network.
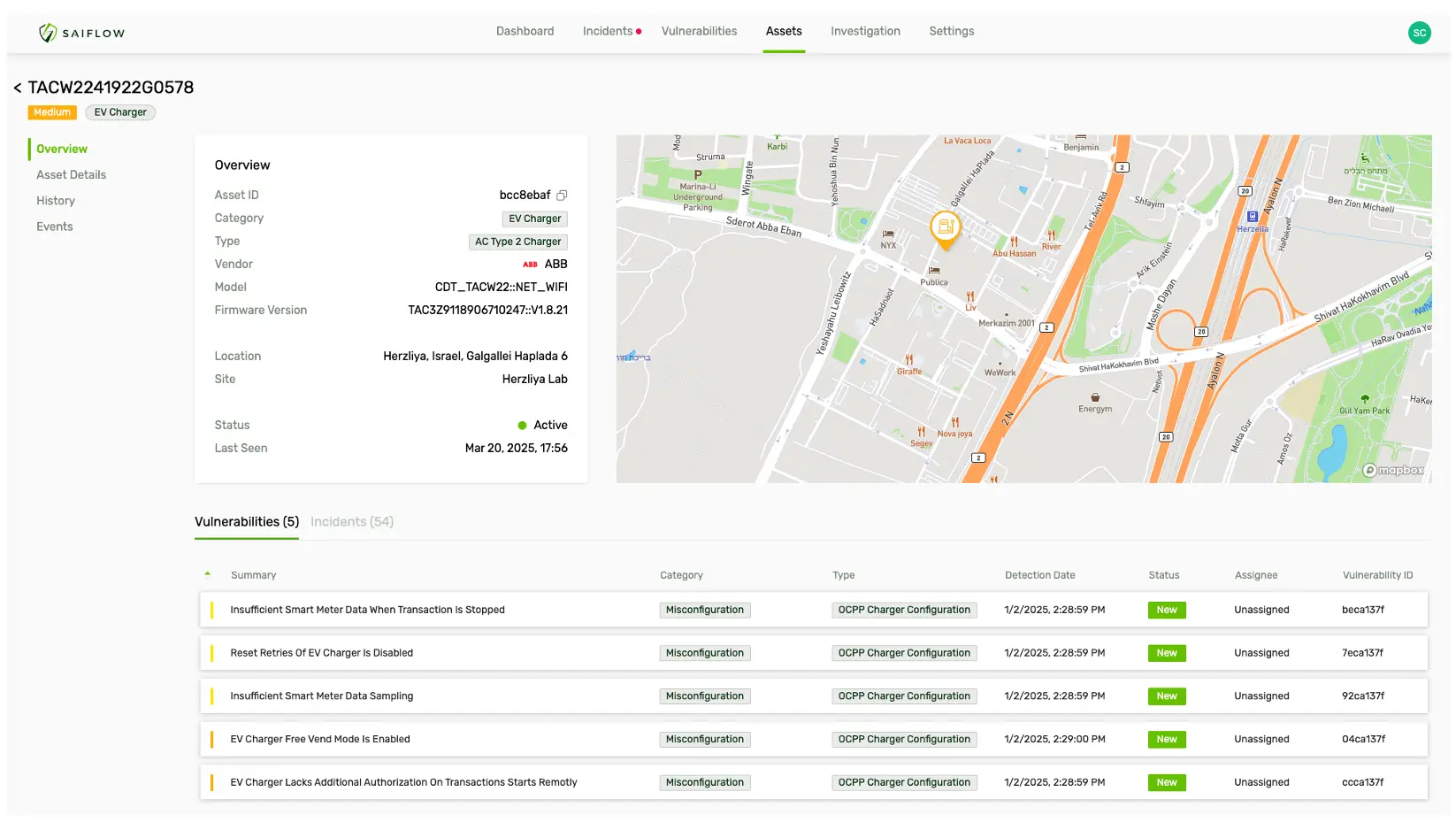
At SaiFlow, we specialize in providing tailored and contextual security solutions that enable full visibility, real-time monitoring, and alerting for all configurations across your EV charging network. Our platform empowers CPOs to ensure that their stations are configured correctly, securely, and consistently, so drivers and operators alike can have a seamless and safe charging experience.